Mumbai: 2019 has been called the “year of ransomware attacks on municipalities,” according to Kaspersky security experts.
This comes after the Kaspersky’s researchers found that at least 174 municipal institutions, with over 3,000 subset organizations, have been targeted by ransomware during this year.
This counts for atleast 60% increase from 2018 data. While threat actors’ demands would sometimes reach up to $5,000,000, actual costs and damages sustained during attacks are estimated to be larger.
Looking back at the past three years, the share of users targeted with ransomware in the overall number of malware detections has risen from 2.8% to 3.5%
The proportion of ransomware targets among all users attacked with malware has been fluctuating, yet appears to be decreasing, with the figure for H1 2019 showing 2.94% compared to 3.53% two years ago.
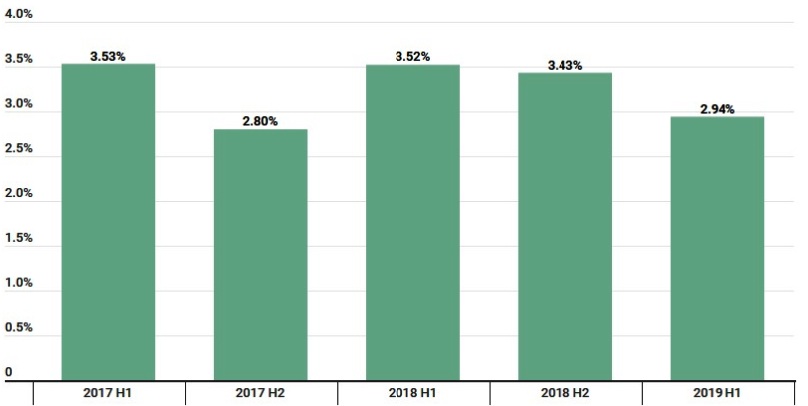
(Source – Securlist.com / Kaspersky)
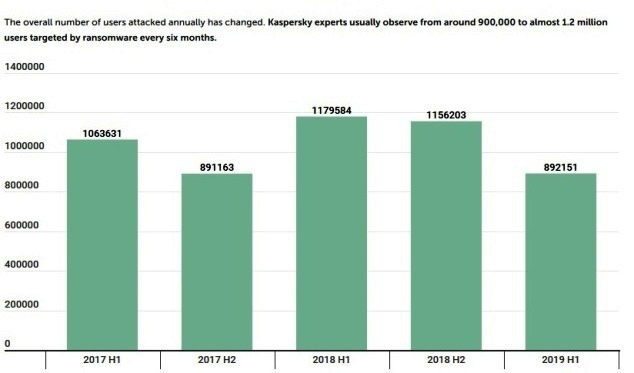
(Source – Securelist.com /Kaspersky)
These are among the main findings of Kaspersky’s Security Bulletin: Story of the Year 2019
Ransomware is a notorious headache for the corporate sector, affecting businesses around the world for a number of years. As if that wasn’t enough, 2019 has seen the rapid development of an earlier trend, where malware distributors have targeted municipal organizations.
Researchers note that while these targets might be less capable of paying a large ransom, they are more likely to agree to cybercriminals’ demands. Blocking any municipal services directly affects the welfare of citizens and results, not only in financial losses but other socially significant and sensitive consequences.
Judging by publicly available information, the ransom amounts varied greatly, reaching up to $5,300,000 and $1,032,460 on average. The researchers noted that these figures do not accurately represent the final costs of an attack, as the long-term consequences are far more devastating.
Kaspersky’s Security researcher Fedor Sinitsyn calls paying extortionists is a short-term solution which only encourages criminals and keep them funded to quite possibly return.
“Once the city has been attacked, the whole infrastructure is compromised and requires an incident investigation and a thorough audit. This inevitably results in costs that are additional to ransom,” says Sinitsy.
“At the same time, based on our observations cities might be sometimes inclined to pay because they usually cover the cyber risks with help of insurance and allocating budgets for incident response,” he adds.
However, according to Sinitsy, the better approach would be also investing in proactive measures like proven security and backup solutions as well as regular security audit.
“While the trend of attacks on municipalities is only growing, it can be stifled and nipped in the bud by adjusting the approach to cybersecurity and what is more important by the refusal to pay ransoms and broadcasting this decision as an official statement,” comments Sinitsy.
Three notorious malware families
The malware that was most often cited as a culprit varies too, yet three families were named as the most notorious, by Kaspersky researchers: Ryuk, Purga and Stop.
Ryuk appeared on the threat landscape more than a year ago and has since been active all over the world, both in public and in the private sector. Its distribution model usually involves delivery via backdoor malware which in turn spreads by the means of phishing with a malicious attachment disguised as a financial document.
Purga malware has been known since 2016, yet only recently municipalities have been discovered to fall victims to this trojan, having various attack vectors – from phishing to brute force attacks.
Stop cryptor is a relative novice as it is only one year old. It propagates by hiding inside software installers. This malware has been popular, number seven in the top 10 most popular cryptors ranking of Q3,2019.
India was attacked by all three groups of ransomware with India being targeted 5.84% by Ryuk, 0.80% by Purga and 10.10% by Stop
(*Percentage of unique users attacked in each country by Stop, relative to all users attacked worldwide by this malware)
To avoid such malware infiltrating organizations, Kaspersky has the following recommendations:
- It is essential to install all security updates as soon as they appear. Most cyberattacks are possible by exploiting vulnerabilities that have already been reported and addressed, so installing the latest security updates lowers the chances of an attack
- Protect remote access to corporate networks by VPN and use secure passwords for domain accounts.
- Always update your operating system to eliminate recent vulnerabilities and use a robust security solution with updated databases
- Always have fresh back-up copies of your files so you can replace them in case they are lost (e.g. due to malware or a broken device) and store them not only on the physical object but also in cloud storage for greater reliability
- Remember that ransomware is a criminal offense. You shouldn’t pay a ransom. If you become a victim, report it to your local law enforcement agency. Try to find a decryptor on the internet first – some of them are available for free here: https://noransom.kaspersky.com
(Image source – Dreamstime)

