Mumbai: A major Twitter hack in the US last Wednesday has once again forced security experts to scrutinize Twitter’s security and approach. Twitter has suffered several hacking incidents and breaches in the past.
And the July 15 hacking attack on Twitter has once again exposed weakness in the overall security and continues to remain a prime concerns for security experts.
The micro-blogging site has a bit of dark history, marred with several incidents of hacking and data breaches, including a recent hack of CEO Jack Dorsey’s Twitter account.
The High Profile Twitter Heck
But this time around attackers targetted verified Twitter accounts of several high-profile personalities and public figures. According to Twitter, around 130 Twitter accounts including top politicians, celebrities and public figures were breached and intruded.

“This is not the first time the privacy of users in the social platform was impacted by its employees, nor the first time that Twitter employees were responsible for sensitive data disclosure,” added Lotem Finkelstein, Head – Threat Intelligence, Check Point Software Technologies.
High Profile Twitter Accounts Compromised
Among them were accounts of former US President Barrack Obama, Democratic Party’s presidential candidate Joseph Robinette Biden Jr., American rapper Kanye Omari West, Microsoft founder and philanthropist Bill Gates, Amazon CEO Jeff Besoz, SpaceX CEO Elon Reeve Musk, Investor Warren Buffet, former New York Mayor Micheal Bloomberg along with tech company Apple.
The recent Twitter hack appears to be no less than any planned massive “coordinated social engineering attack” that may be part of some bigger bitcoin scam.
Fake Tweets From Verified Accounts & The Bitcoin Scam
After hacking into high profile Twitter handles on July 15, the hackers had successfully posted identical messages from some of those compromised accounts. These messages asked individuals to deposit some $1000 into a specific bitcoin wallet address. And then would get doubled the money in return.
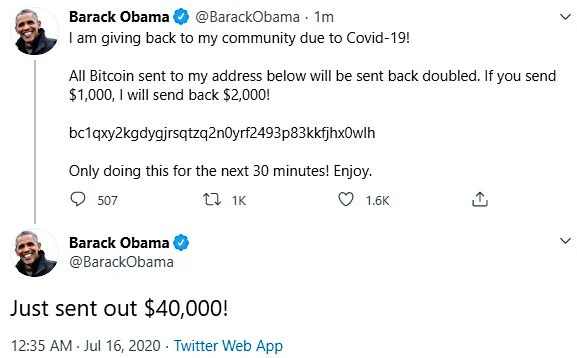
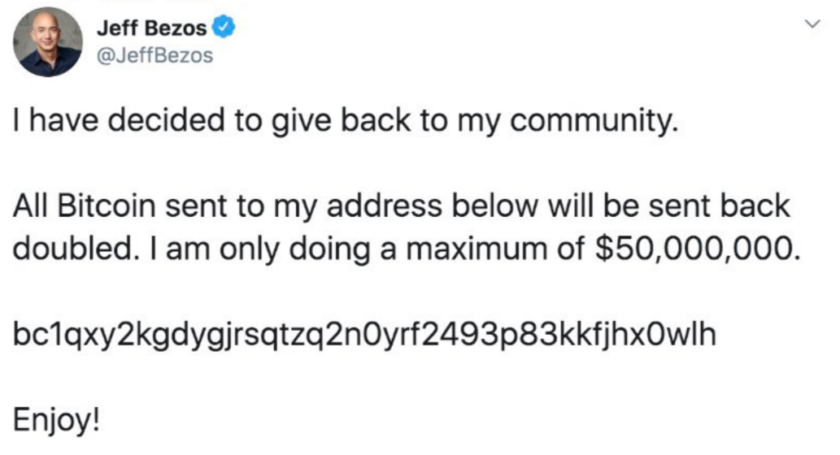
“Of course, it’s all a pack of lies – after all, if someone already had $1000 to gift you, why wouldn’t they just send it to you, instead of making you pay in $1000 first and then giving you your money back plus another $1000?” Paul Ducklin, Sophos‘ Head – Technology in Asia Pacific commented.
This act had continued for some hours on Wednesday afternoon, before Twitter could actually take control of this situation and those compromised accounts. After that Twitter had suspended most of the verified user accounts across the globe for some time as part of security measures.
It is believed that amidst this breach a specific bitcoin wallet account had received hundreds of thousands of dollars based on those fake messages posted via hacked accounts.
The reason, why People did put money into a specific bitcoin wallet was because fake tweets were posted from verified accounts, according to Sopho’s Ducklin.
“Nevertheless, these tweets really did come from verified accounts, so you can see why people might fall for this – it’s not like receiving an email that is signed off “Elon Musk” if the tweet genuinely seems to have come from his account,” explained Ducklin.
Twitter’s Security Exposed & Penetrated
What makes this Twitter hack more alarming is the fact the hackers or unknown individual/s behind this attack had access into Twitter’s backend systems and controls. That too, right at the systems administration level.
Making it a bit easy for them to bypass the existing layer of security in any account-based protected by password, coupled with two-factor authentication (2FA) mechanism. This does lead to a strong suspicion that this hacking incident may be an act of insider involving Twitter’s employees.
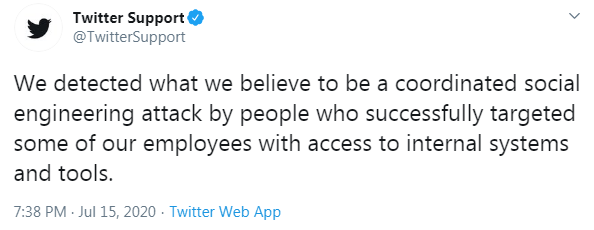
As part of its internal investigation, Twitter revealed that the hacking incident was a “coordinated social engineering attack” by some people or hackers and its employees.
“However, these scammers will only succeed if people fall for their unlikely messages – which rely on people suspending their disbelief simply because the tweet comes from a celebrity or someone they are inclined to trust,” commented Ducklin.
“We detected what we believe to be a coordinated social engineering attack by people who successfully targeted some of our employees with access to internal systems and tools,” Twitter said in a statement.
“Some high-level employees at Twitter were targeted by social engineering campaigns to gain access to high profile accounts. If purely digital companies like Twitter can be breached through social engineering attacks, then other organizations and individuals are not safe either,” said Himanshu Dubey, Director – Quick Heal Security Labs.
Cybersecurity is everybody’s responsibility according to Dubey and employees can be an organisation’s best defence. “Hence, employee training on cybersecurity and good hygiene principles is absolutely must,” added Dubey.
Twitter has continued its investigation and security measures post the June 15 hacking attack and in the mean time, it did reveal the number of accounts that were compromised.
“Based on what we know right now, we believe approximately 130 accounts were targeted by the attackers in some way as part of the incident. For a small subset of these accounts, the attackers were able to gain control of the accounts and then send Tweets from those accounts,” Twitter informed.
So far Twitter has shared details of breach incident in bits and pieces as it continues the internal investigation. But that is more than enough for security experts and US government officials to question and raise doubts on the San Francisco headquartered company.
“Although Twitter has not yet shared the full details of this incident, we can see that different root causes in previous cases have led to similar results,” Check Point’s Finkelstein compared the outcomes of the breach incidents in past and a recent one.
Finkelstein has expressed some concerns against the NYSE listed tech company ‘s challenge in restricting access to internal assets. “Whether it is disgruntled employees or tailored social engineering attacks, the true problem is the difficulty in limiting access to internal assets and preventing them from becoming a single point of failure,” he pointed out.
Interestingly, though Finkelstein has pointed to the problem that Twitter is grappling with, still he reckoned that this time around Twitter seems to be taking action to prevent such incidents from occurring again in the future, by making tools such as the one presumably used in this attack less accessible:
Twitter’s compromise, according to Finkelstein shows that in today’s world of increasing data loss events, organisations have little choice but to take action to protect sensitive data.
“Confidential employee and customer data, legal documents, and intellectual property are being exposed to unwanted parties daily,” Finkelstein raised his concerns on today’s situation of data getting exposed to unwanted parties.
While, Twitter continues its internal investigation on the latest breach, but it is very clear that Twitter certainly need to re-look its security mechanism in all aspect including its staffs.
The recent Twitter hack is a real-life example of how the combination of a coordinated attack and social engineering can prove dangerous for social media platforms and its users. Other social media platforms can learn a lot from Twitter hack to strengthen and enhance their security postures and mechanism.
(Image credit – TechCrunch)

