Singapore: Malware and ransomware attack pose a major security challenge for developing markets across Asia Pacific. While developed markets struggle with increased drive-by download attack volumes, according to Microsoft Security Endpoint Threat Report 2019.
Markets across Asia Pacific continued to experience a higher-than-average encounter rate for malware and ransomware attacks – 1.6 and 1.7 times higher respectively than the rest of the world. This is despite a 23 and 29 percent overall decline across these two threat vectors when compared to the 2018 findings.
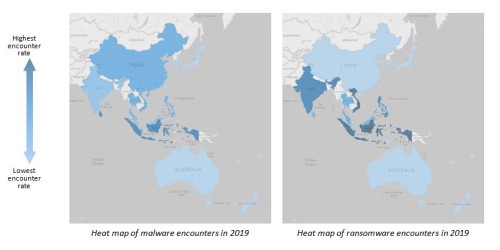
Indonesia, Sri Lanka, India, and Vietnam among the developing countries were most vulnerable to malware and ransomware threats in 2019, revealed the report.
Microsoft conducts this research annually to identifying cyber threats and building cyber resilience across the region.
“Often, high malware encounters correlate with both piracy rates and overall cyber hygiene, that includes regular patching and updating of software,” said Mary Jo Schrade, Assistant General Counsel, Microsoft Digital Crimes Unit – Microsoft Asia.
“Countries with higher piracy rates and lower cyber hygiene tend to be more severely impacted by cyberthreats. Patching, using legitimate software, and keeping it updated can decrease the likelihood of malware and ransomware infections,” added Schrade.
The research identified that countries with lower piracy rates and stronger cyber hygiene practices have witnessed a significant decline in attacks. Specifically, malware and ransomware threat encounter rates in Japan, New Zealand, and Australia, were three to six times lower than the regional average.
Despite the low threat encounters observed in developed countries, Schrade urged all businesses to remain vigilant.
“Cybercriminals do not stand still. We are witnessing attackers pivoting away from conventional methods, and shifting towards customized campaigns, targeted at specific geographies, industries, and businesses,” he informed.
“By relying on cloud technology and developing a comprehensive cyber resilience strategy, organizations can effectively bolster their cybersecurity strategies,” explained Schraded.
Cryptocurrency mining on the rise in developing markets
India, Indonesia, and Sri Lanka recorded the highest cryptocurrency mining encounters in Asia last year. During such attacks, victims’ computers are infected with cryptocurrency mining malware, allowing criminals can leverage the computing power of their computers without their knowledge.
While, Hong Kong, Japan and Singapore were among the countries which recorded declining encounter rate.
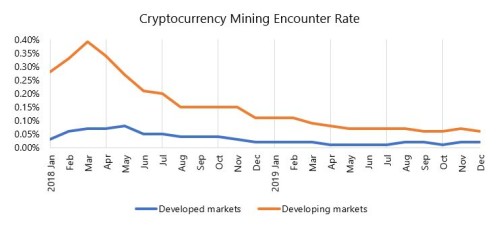
“Cybercriminals are usually incentivized by quick financial gains. We believe that the recent fluctuations in the value of cryptocurrency and the increased time required to generate it, has perhaps led to them focusing on other forms of cybercrime,” pointed out Schraded.
Drive-by download attack volume reaches parity with global average but continue to challenge regional business and financial hubs
The Drive-by download attack volume in Asia Pacific has converged with the rest of the world at 0.08, following a 27 percent decline from 2018.
These attacks involve downloading malicious code onto an unsuspecting user’s computer when they visit a website or fill up a form. The malicious code that is downloaded is then used by an attacker to steal passwords or financial information.
Despite the general fall in drive-by download attacks across the region, the study found that regional business hubs, Singapore and Hong Kong, recorded the highest attack volume in 2019, over 3 times the regional and global average.

“We usually see cybercriminals launch such attacks to steal financial information or intellectual property. This is a likely reason why regional financial hubs recorded the highest volume of such threats. The high attack volume in these markets may not necessarily translate into a high infection rate, perhaps due to their good cyber hygiene practices and use of genuine software,” explained Schrade.
Cybersecurity in the age of COVID-19
With the turn of the new year, COVID-19 has changed the landscape and remains the top-of-mind concern for individuals, organizations, and governments around the world.
Since the outbreak, Microsoft Intelligence Protection team’s data has shown that every country in the world has seen at least one COVID-19 themed attack, and the volume of successful attacks in outbreak-hit countries seems to be increasing, as fear and the desire for information grows.
Of the millions of targeted phishing messages seen globally each day, roughly 60,000 include COVID-19 related malicious attachments or malicious URLs. Attackers are impersonating established entities like the World Health Organization (WHO), Centers for Disease Control and Prevention (CDC), and the Department of Health to get into inboxes.
“According to our data, we found that COVID-19 themed threats are mostly rethreads of existing attacks that have been slightly altered to tie to the pandemic,” said Schrade.
“This means that attackers have been pivoting their existing infrastructure, like ransomware, phishing, and other malware delivery tools, to include COVID-19 keywords, to capitalize on people’s fear. Once users click on these malicious links, attackers can infiltrate networks, steal information and monetize their attacks,” he concluded.
The research covered a total of 15 markets across Asia Pacific, including developing markets China, India, Indonesia, Malaysia, Philippines, Sri Lanka, Thailand and Vietnam; and developed markets Taiwan, Singapore, New Zealand, Korea, Japan, Hong Kong, Australia. Markets were categorized with reference to IMF’s World Economic Database 2018.

