Mumbai: Kaspersky has released a report on major initial vectors of ransomware attacks in 2022. The report showed that the majority of these attacks in 2022, started with the exploitation of public-facing applications, data from compromised user accounts and malicious emails.
According to the IT Security Economics report, over 40% of companies faced at least one ransomware attack in 2022 and SMBs spent an average of $6,500, whilst enterprises paid out 98,000$ for the recovery. These figures reveal that ransomware attacks are still widespread and can hit any company, at any time.
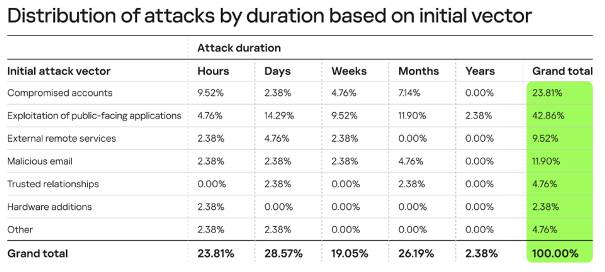
Statistics from the Kaspersky Incident Response Analyst Report ‘The nature of cyber incidents’ showed that almost 43% of ransomware attacks investigated by Kaspersky experts in 2022 started with public-facing apps exploitation, followed by data from previously compromised user accounts and malicious emails with 24% and 12% respectively. The attackers’ goal was not extortion or data encryption, but the mining of personal data, intellectual property, and other sensitive information.
In most of these cases, known credentials had already been compromised and there were no artefacts left to analyse by the time the crime was discovered due to log rotation policies, so it was not possible to investigate how this data was leaked.
The report also revealed that the longest-running ransomware attacks began with the exploitation of public-facing applications, with just over 2% of them lasting for a year and more.
“Continuing security issues with passwords, software vulnerabilities and social engineering become initial access vectors for attackers and provide them endless ways to perpetrate ransomware activities,” said Konstantin Sapronov, Head of Global Emergency Response Team – Kaspersky.
“To minimise the potential for such activities, it’s important for businesses to set up and control a password policy, patch management, raise employee awareness and take regular anti-phishing measures,” added Sapronov.

