Singapore: Small bit-and-piece cyberattacks including DDoS attacks jumped 233% in the first half of 2021, revealed Nexusguard’s Threat Report FHY 2021.
With no respite from the pandemic in 2021, hackers experimented with new attack patterns to avoid signature-based detection. In 1H 2021, over 99% of all DDoS attacks were smaller than 10Gbps, as Nexusguard had predicted in 2020.
These small, nimble attacks can cripple communications service providers (CSPs) and Internet service providers (ISPs) if they leave detection to a threshold or signature-based methods alone.
Small bit-and-piece cyberattacks
Nexusguard researchers found that the attackers are continuing to diversify their approaches with small bit-and-piece cyberattacks to bring down target networks and infrastructures. Over 95% of attacks were smaller than 1Gbps each launched using readily available and inexpensive DDoS-for-hire services believed Nexusguard analysts.
Rather than launching large bandwidth attacks against their targets, researchers noted that perpetrators chose to employ attacks using high packet-rate loads of small-sized traffic from DDoS-for-hire services, with the aim of evading DDoS (distributed denial of service) mitigation detection systems.
“The high level of intricacies behind communications service provider networks causes them to generally allow all types of traffic to pass through, which leads to smaller or spoofed types of attacks to strike undetected,” said Juniman Kasman, CTO – Nexusguard.
“Behavioural detection and mitigation approaches are strongly recommended for targeted networks. Since they can compare peacetime with battles and take a wider range of factors into consideration than anomalous thresholds or attack signatures,” added Kasman.
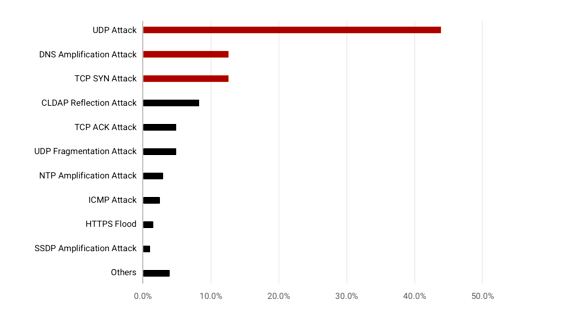
Traffic spoofing and UDP-style attacks were popular in 1H 2021, with an 84% jump in UDP attacks compared to the previous six months. Nexusguard observed several types of UDP attacks in use, one of which can cause “Black Storm” attacks theorised in recent research.
DDoS attacks hit China Telecom, China Unicom, Vodafone Türkiye, Türk Telekom and Turkcell İletişim Hizmetleri A.S. They suffered from the highest concentrations of malicious traffic, as per Nexusguard researchers.
Nexusguard advises CSPs to use deep learning-based detection methods, which can help CSPs analyze huge amounts of data quickly and accurately while overcoming the inefficiencies inherent in threshold or signature-based methods.

